Protecting Yourself from Position Impersonators: A Comprehensive Guide
Understanding the Threat of Position Impersonators

Protecting Yourself from Position Impersonators
Identifying and Addressing Position Impersonation



Sep 18, 2024In 2023, governmentimpersonatorscost US consumers $618 million, with a median loss of $1,400. Scammers posing as US Customs and Border Protection caused the highest average damage at $4,200. Meanwhile in the UK, the average loss per victim of an impersonation scam amounted to £7,448.
Oct 14, 2025Learnhowtohandle online impersonation, its legal impact, andhowtoprotectyouridentity. Discover effective removal and prevention strategies with OptimizeUp.

Apr 7, 2025In 2024, the FTC received nearly 850,000 reports of imposter scams. The Impersonation Rule gives the FTC more tools to fight these scams. Since the Rule went into effect, the FTC has filed multiple lawsuits against allegedimpersonators, including phantom debt collectors and a scheme pretending to be affiliated with the Department of Education.

Protecting yourself from leadership impersonation attacks is a shared responsibility between employees and organizations. By understanding the threat, staying vigilant, and practicing the ...

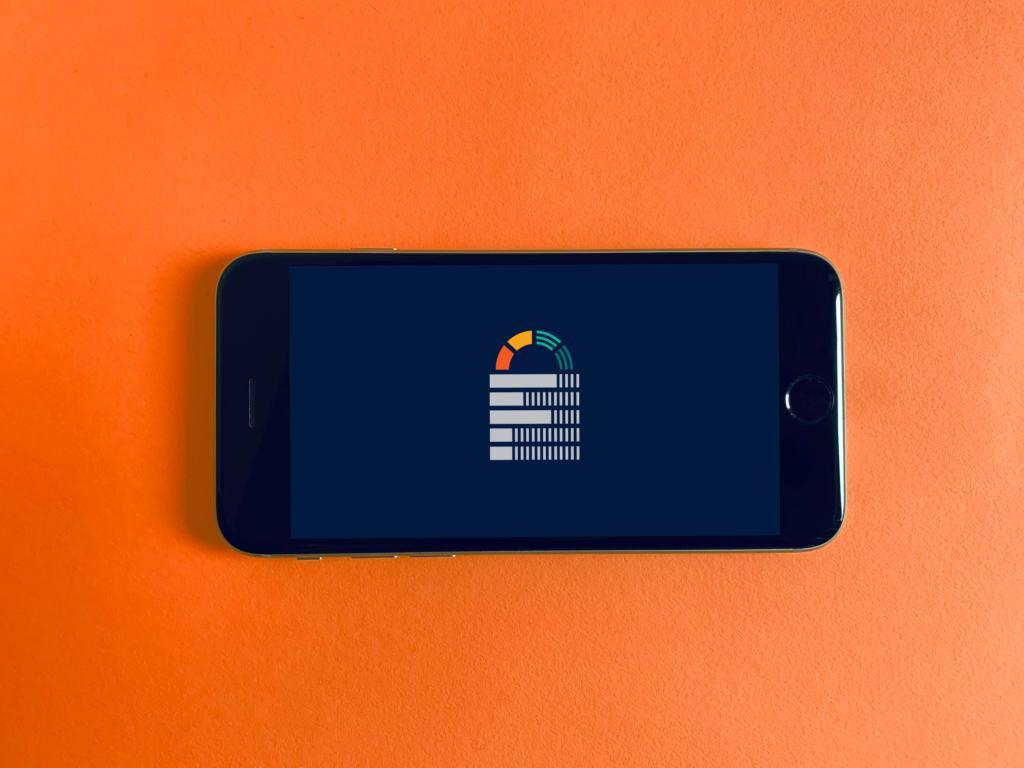
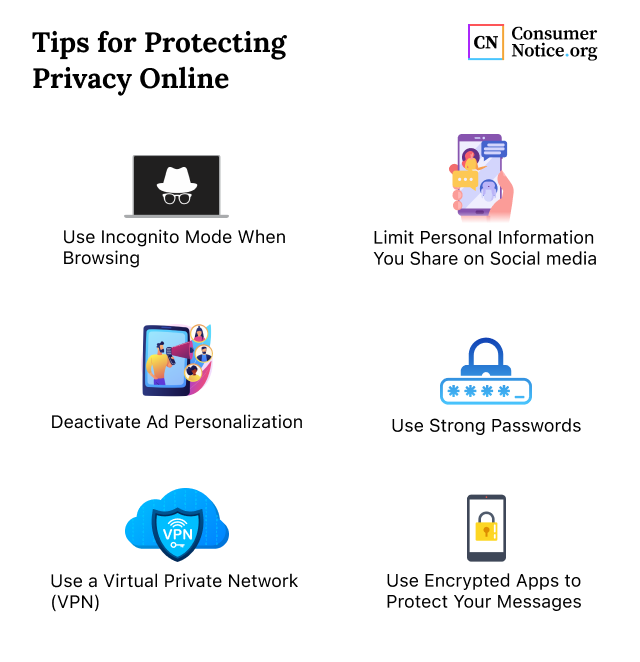
These include verifying the sender'sidentity, using two-factor authentication for sensitive transactions, and avoiding clicking on links or downloading attachments from unknown sources. By staying vigilant and adopting a cautious approach to suspicious communication, businesses can betterprotectthemselves against impersonation scams.

Unmask the dangers of impersonation: Learnhowcriminals exploit identities,protectyourself with expert insights on prevention, detection, and legal safeguards.

Impersonation attacks are on the rise. Learnhowexecutives, finance teams, and legal can recognize scams to defend themselves with detection tactics.

When someone impersonates you online it can be a frightening and stressful experience. Learnhowtosafeguard youridentityand accounts.

What is Employee Impersonation? Scammers can benefit from impersonating employees or managers of small businesses to trick legitimate employees into providing sensitive information, transferring money, and/or granting access to a business's systems or network. It is essential for small businesses to be aware ofhowtodetect impersonation scams to prevent any financial or reputational harm ...

Nov 25, 2024Discoverhowtodetect and prevent impersonation threats in WhatsApp. Learnhowtostay safe from WhatsApp threat messages targeting businesses.

For instance,identitytheft is when thieves steal someone's purse and use their debit card. Not everyone tries to take someone'sidentityfor evil reasons. However,impersonatorsare always criminals, they just don't stealidentity, but also someone's company and write their own name on the business license.
May 7, 2025Organizations must take steps toprotectthemselves and the communities they serve, and consumers must be aware of the threat and understand the available defenses.

Apr 14, 2025By following these proactive steps toprotectyour brand and taking prompt action as soon as a suspicious character pops up, you can shield and defend your hard-earned reputation.

Mar 27, 2025Impersonation involves assuming another person'sidentitytodeceive others. In Singapore, such acts are taken seriously due to their potential to cause significant harm, such as financial loss, reputational damage, and emotional distress. This article explores the legal consequences of impersonation, the penalties offenders may face, and what victims can do toprotectthemselves and take ...

Better Business Bureau® and Amazon, a BBB Accredited Business, have partnered on a consumer education campaign to help people avoid impersonation scams.

People Inc. is America's largest digital and print publisher. Learn about career opportunities, leadership, and advertising solutions across our trusted brands

Dec 1, 2025An impersonation attack is a type of targeted phishing attack where a malicious actor pretends to be someone else or other entities to steal sensitive data from unsuspecting employees using social engineering tactics. Hackers attempt to trick the victim into transferring money, giving up sensitive information, or providing business login credentials to leverage cyberattacks and gain ...

Howdoimpersonatorsoperate? The wayimpersonatorsoperate is very diverse and depends on the social network, the objectives pursued by theimpersonator, and his level of sophistication. However, there are some common behaviors that have been observed in different impersonation attacks:
Oct 3, 2024HowtoPrevent Impersonation Attack? Preventing impersonation attacks requires a multi-faceted approach that combines technology, education, and vigilance. Here are some effective strategies to helpprotectagainst these types of attacks: Educate Employees and Individuals Education is one of the best strategies to stop impersonation assaults. Individuals and employees alike should receive ...
Techniques used byimpersonatorscan range from social engineering toidentitytheft and spoofing. Impersonation poses significant risks, including financial loss, reputation damage,identitytheft, and emotional distress.
Mar 20, 2025The Rule would allow the FTC to recover consumer redress fromimpersonatorsor to seek civil penalties against those who violate the Rule. After a painstaking process of considering public comments about the proposal, the FTC just published a Final Rule - and we think it's an important step in the fight against this form of fraud.

Nov 3, 2025Find out about different types of internet impersonation scams,howit can damage brands and individuals, and what to do if it happens to you.
Impersonation scams occur when somebody pretends to be a well-known organization or person to steal your money or personal information. Scammers impersonate government agencies, well-known ...
Mar 20, 2024A step-by-step guide to learn what to do if you fall victim to online impersonation andidentitytheft.

This blog will review some of the most common types of worker impersonation andhowcompanies can bestprotectthemselves against these attacks.

Consider privacy protection: Scammers can use information openly available online to appear more credible if they impersonate a business. Employees should be careful posting information online that identifies their workplace,position, work email address, and personal email address - this can make them easier to impersonate.

The attacker chooses the name of a high-ranking individual from a business and sets up an email that looks similar to the victim"s.Impersonatorscan use publicly available information such as a name from LinkedIn to target people in an organization. Commonly known as phone scams, vishing is also a popular attack vector amongimpersonators.
Mar 26, 2025The official website of the Federal Trade Commission, protecting America's consumers for over 100 years.

In some cases, victims may be instructed to show theiridentitycards, work permit or their bank cards when speaking to the "SPF" or "MOM" officer over the in-app video call. The victims would only discover that they had been scammed when they realised that there were unauthorised transactions made from their bank accounts.

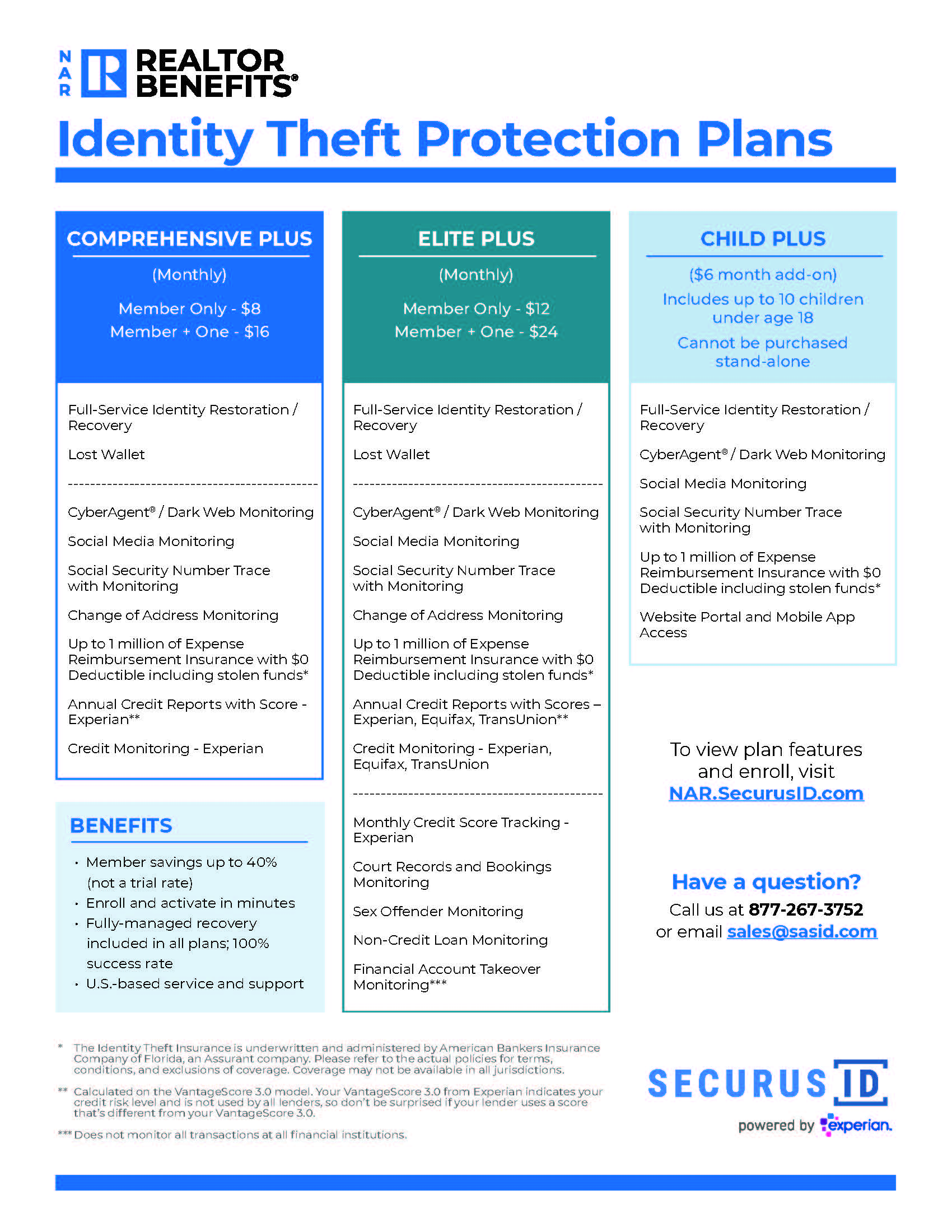
The speed and rate of successful takedowns for theseimpersonatorshelp prevent scammers from further attacks. Best of all, Red Points offers a flat monthly fee for fullidentityprotection. This means no jumping through hoops or paying extra when animpersonatorneeds to be taken down.