Be Cautious: Detecting Phishing Spam Emails
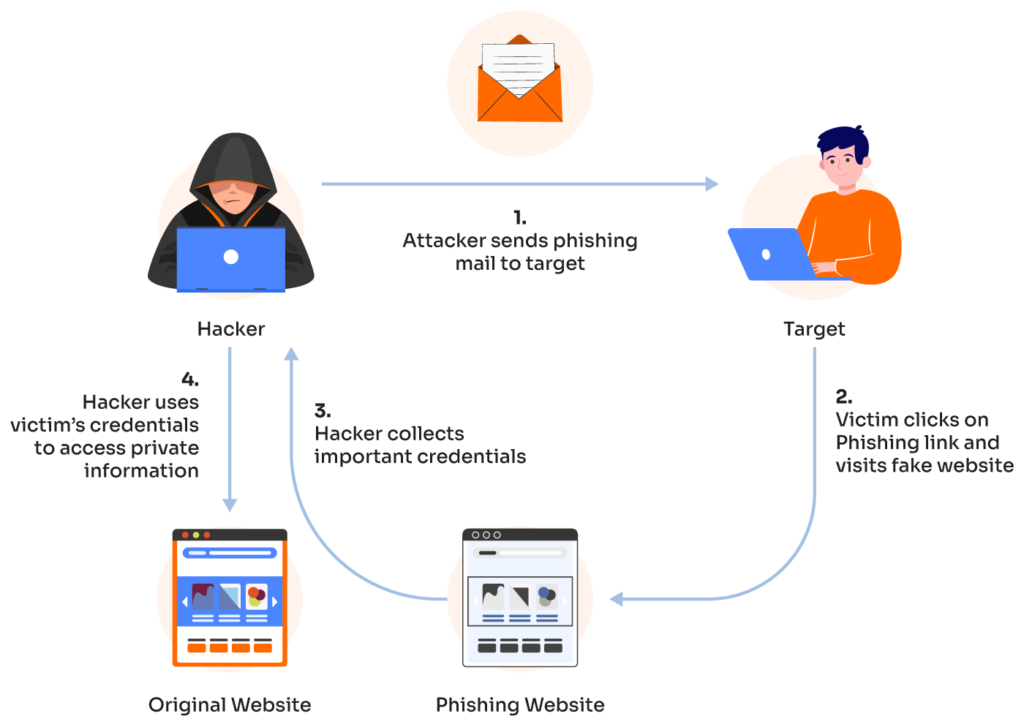
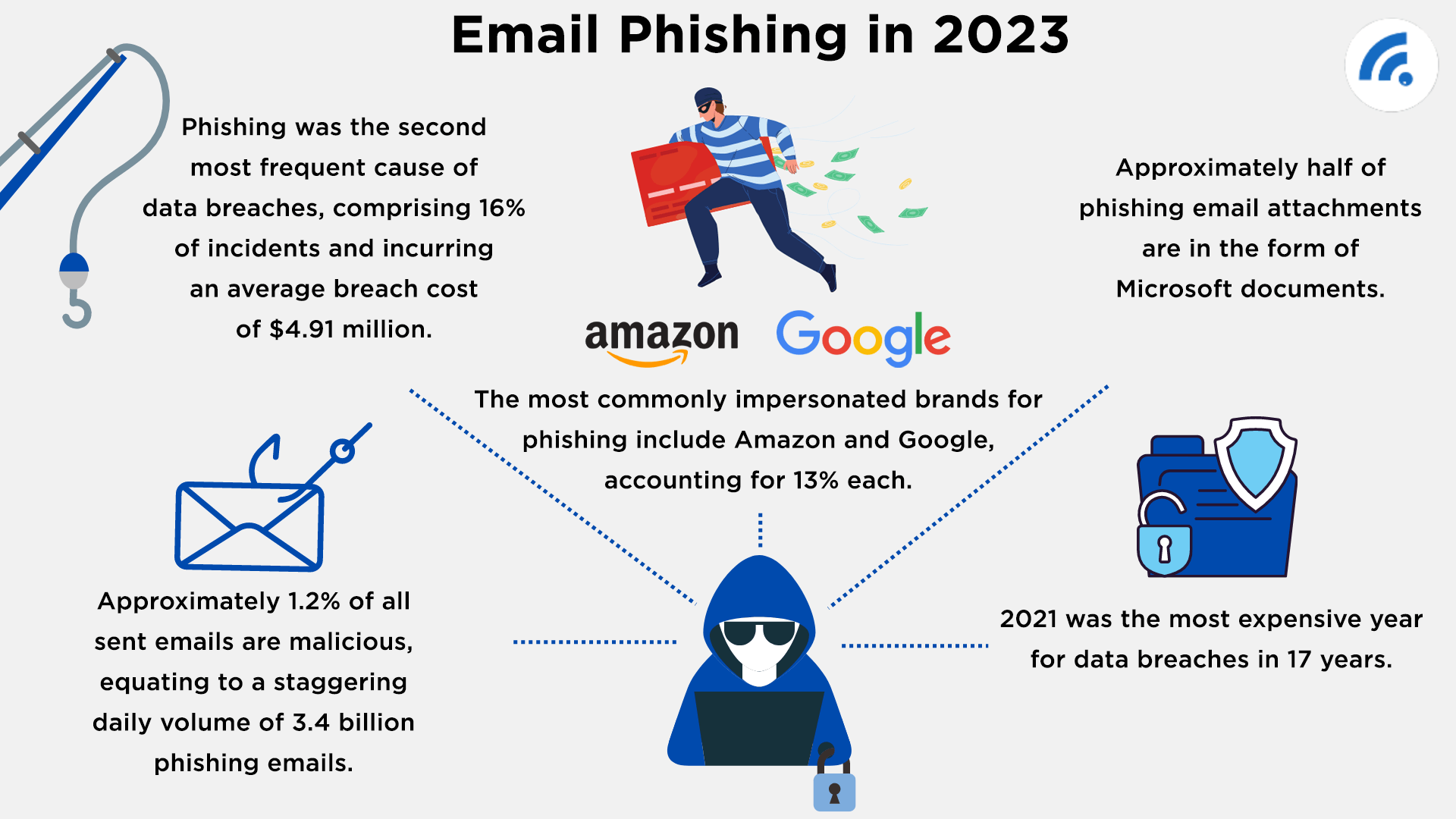
Phishing scammers use email or text messages to try to steal your passwords, account numbers, or Social Security numbers. If they get that information, they could get access to your email, bank, or other accounts. Or they could sell your information to other scammers. Scammers launch thousands of phishing attacks like these every day — and they're often successful. With over 3 billion phishing emails sent every day, your employees need to know how to recognize phishing emails and take appropriate action to protect your organization from attack.Identifying the Common Threats
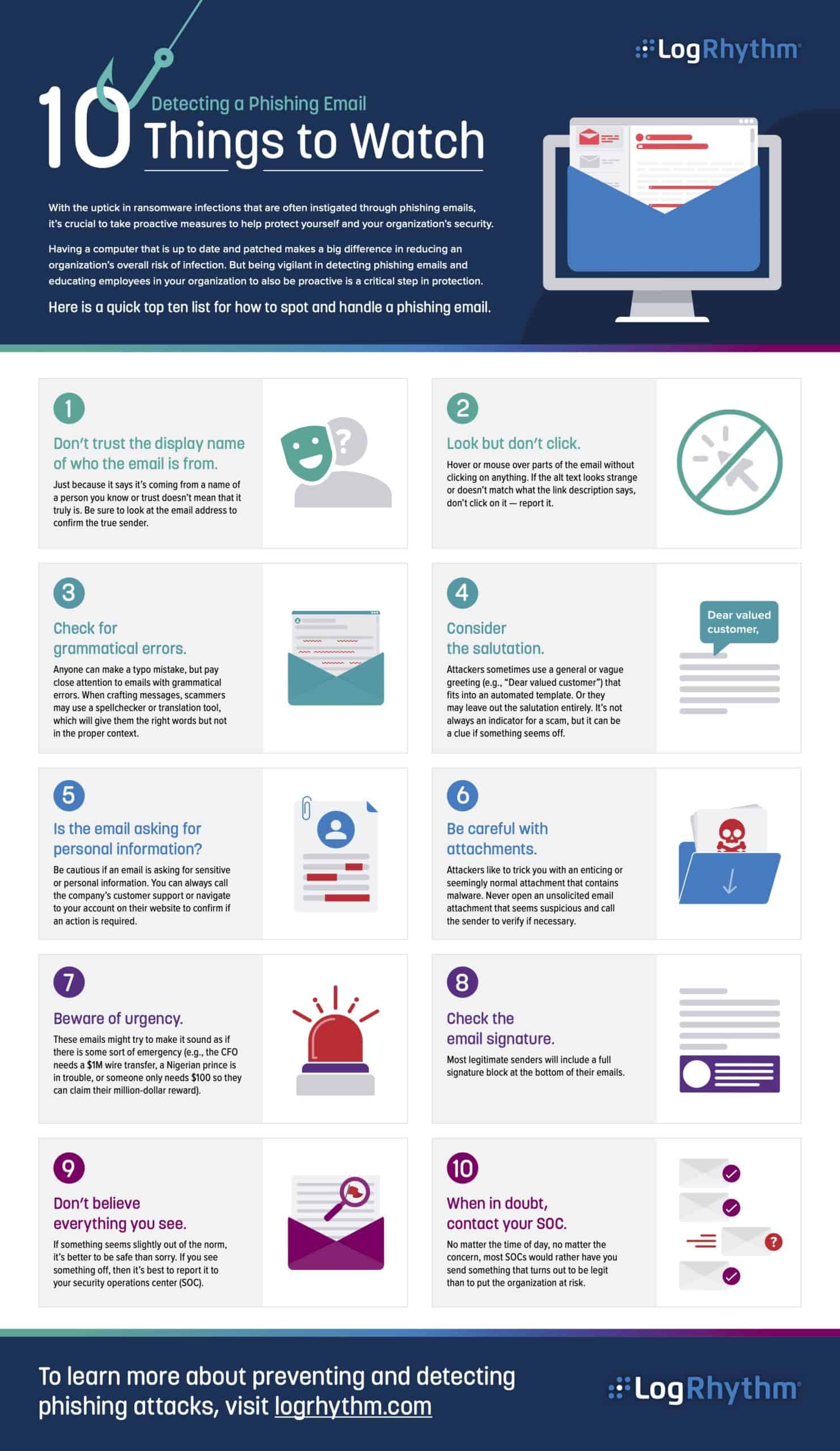
Since over 3 billion phishing emails are sent every day, it's essential to learn how to recognize phishing emails and prevent these malicious attempts. Here are some common signs of a phishing attack:- Urgent or emotionally appealing language
- Requests to send personal and financial information
- Untrusted shortened URLs
- Misspelled or generic greetings
- Poor grammar or sentence structure
- Unsolicited links or attachments
- Requests to verify account information
- Unregistered or unknown sender domains
Suspicions Signs of a Phishing Attack
What to Do If You Suspect a Phishing Email
If you suspect a phishing email, you can take several steps to protect yourself and your organization:- Do not respond to the email
- Do not click on the link or download any attachments
- Report the email to the organization if it's a scam
- Forward the email to your IT department or security team
- Change your passwords and monitor your accounts
Protecting Yourself from Phishing
Furthermore, visual representations like the one above help us fully grasp the concept of Detecting Phishing Spam Emails.
To avoid phishing attacks, you should:- Be cautious with links and attachments
- Verify sender information and URLs
- Keep software and browsers up to date
- Use antivirus software and a reputable firewall
- Enable two-factor authentication
- Use a reputable email client and spam filter
Detecting Phishing Spam Emails
In order to detect phishing spam emails, you can use various tools and technologies, including:- Machine learning algorithms to identify patterns in phishing emails
- Phishing detection software and apps
- AI-powered threat detection platforms
- Domain intelligence and security checks
- Real-time threat detection and email routing