How to Protect Identity from Visitors Areas
As a business owner or facility manager, ensuring the safety and security of your workplace is crucial. One of the most significant concerns is protecting your employees, assets, and sensitive information from unauthorized visitors. In this article, we will explore the importance of implementing effective visitor management practices to safeguard your business from potential threats.
The Risks of Not Verifying Visitor Identity
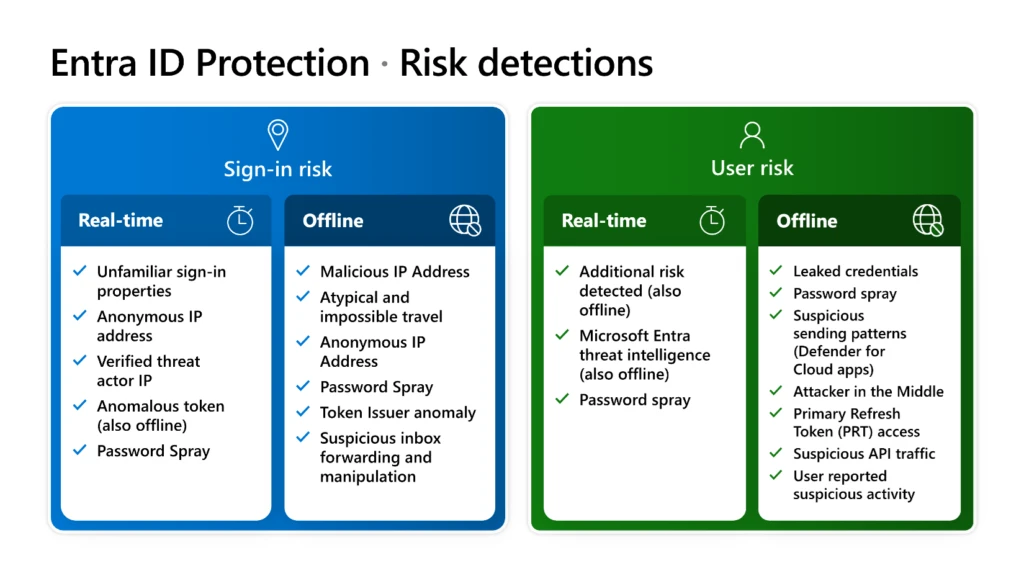
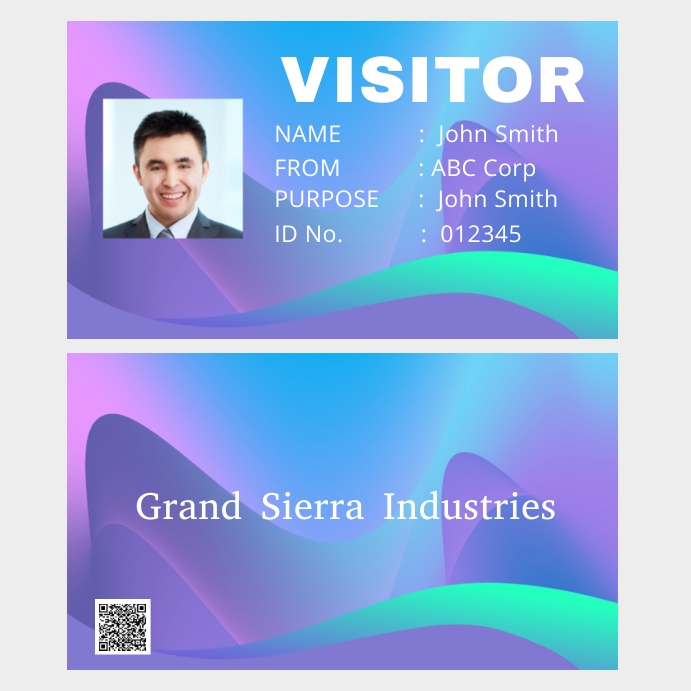
Not verifying the identity of visitors can open the door for unauthorized individuals to gain access to sensitive areas, putting your assets, employees, and data at risk. Unverified visitors can also lead to security breaches, data compromise, and intellectual property theft. A robust visitor management system can help prevent these risks by ensuring that only authorized individuals gain access to your premises.
Implementing Effective Visitor Management
.jpg)
As we can see from the illustration, How To Protect Identity From Visitors Areas has many fascinating aspects to explore.
- Implementing a visitor management system can be a relatively low-cost but high-impact element of layered security.
- By combining visible identification, digital visitor logs, access integration, and privacy-aware processes, organizations can gain clearer accountability, faster incident response, and reduced risk of unauthorized entry.
- Revisioning campuses, offices, and facilities with easy-to-read, detailed maps and visitor signage helps direct visitors to receptionist / guest control area.
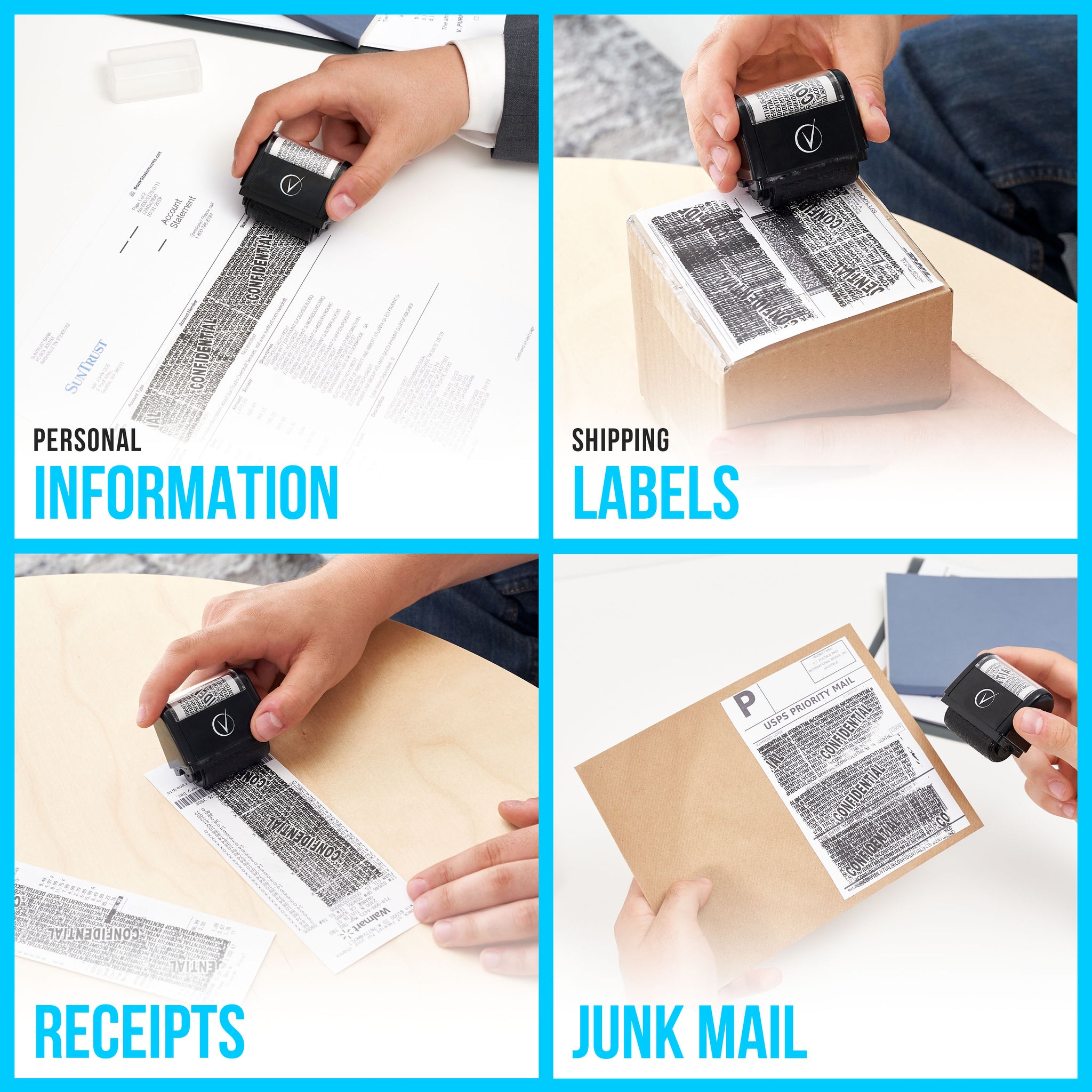
Protecting Visitor Data
In today's digital age, protecting visitor data is crucial to prevent identity theft, data breaches, and other security threats. A well-designed visitor management system should include features such as:
- Self-service registration and online sign-in capability, confronting immediate authority with electronic access lists and sequentially numbered guest bans
- Secure storage of visitor data, access only to participants registered or professionally authorized
- Meeting confidentiality and data protection compliance through visitor agreements

Moving forward, it's essential to keep these visual contexts in mind when discussing How To Protect Identity From Visitors Areas.
Workplace Visitor Policy
A workplace visitor policy sets guidelines for receiving visitors at company premises. The policy should aim to ensure safety, prevent distractions, and protect company property. The policy should cover personal visitors, contractors, vendors, and other types of visitors, detailing their access rights, responsibilities, and expected behavior.